Microsoft Entra ID (formerly Azure AD)
Enterprise integrationAutomatically provision and (most importantly) deprovision DatoCMS users using your centralized Microsoft Entra ID account
Automatic user provisioning is supported for the DatoCMS application.
This enables Microsoft Entra to:
Add new users to DatoCMS
Update users’ profile information in DatoCMS
Deactivate users in DatoCMS
Push groups and memberships to DatoCMS
Features
The following provisioning features are supported:
Create User - Creating a new user in Microsoft Entra and assigning them to the DatoCMS application will create a new user in DatoCMS.
Update User Attributes - Updates to a user in Entra will be pushed to DatoCMS.
Deactivate Users - Deactivating the user or disabling the user's access to DatoCMS within Microsoft Entra will deactivate the user in DatoCMS.
Reactivate Users - User accounts can be reactivated from Microsoft Entra.
Push Groups - Groups created in Microsoft Entra can be pushed to DatoCMS. Attributes pushed include name and group members.
Delete Groups - Groups deleted or removed from the DatoCMS application within Microsoft Entra will be deleted within DatoCMS.
Prerequisites
Single Sign-On is only available for Enterprise plans.
Configuration Steps
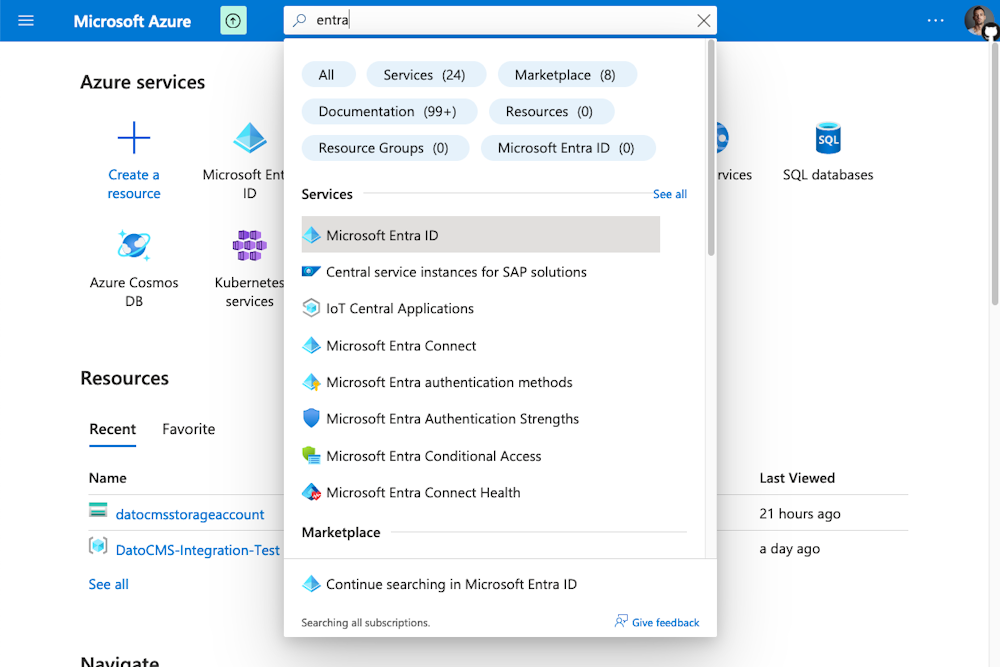
Inside your Microsoft Azure dashboard search for Microsoft Entra ID and enter the service:
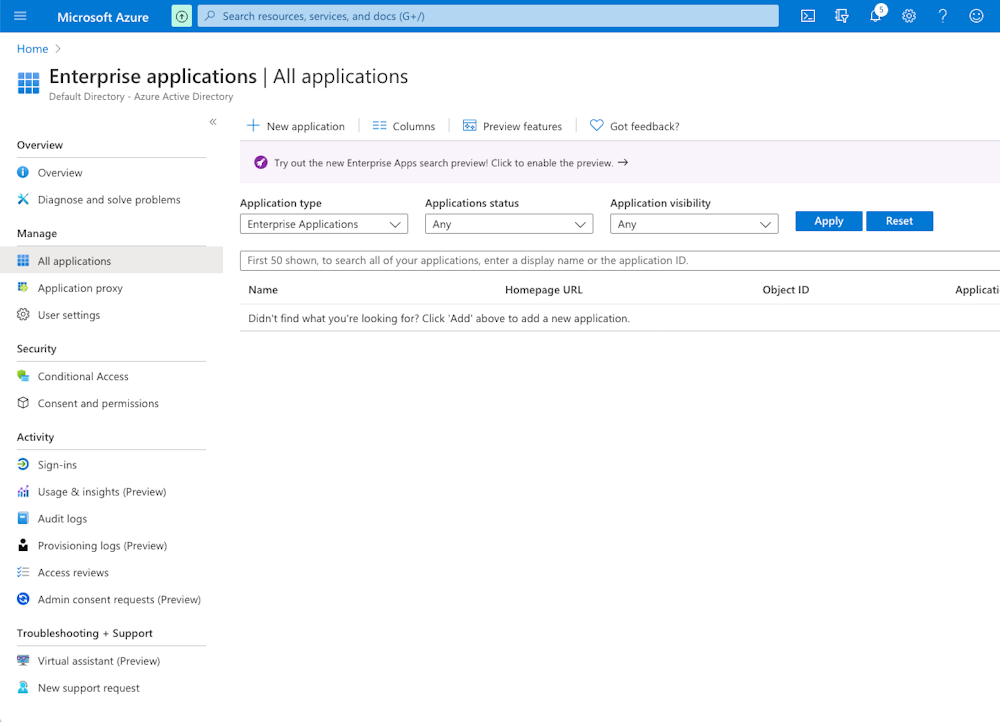
Enter the Enterprise Applications section, then click the New Application button:
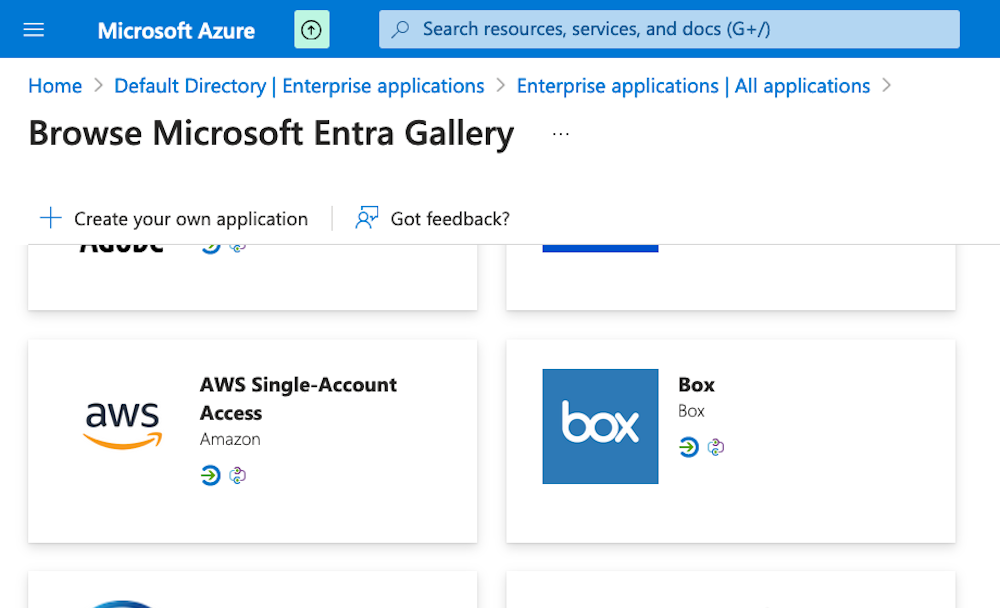
Select Create your own application:
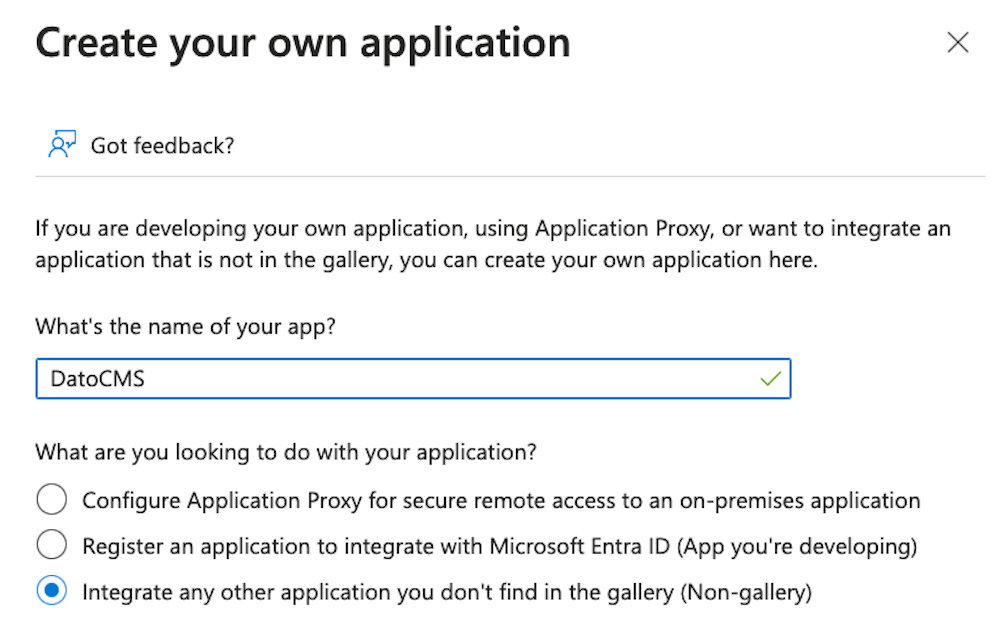
Name your application DatoCMS and click the Create button:
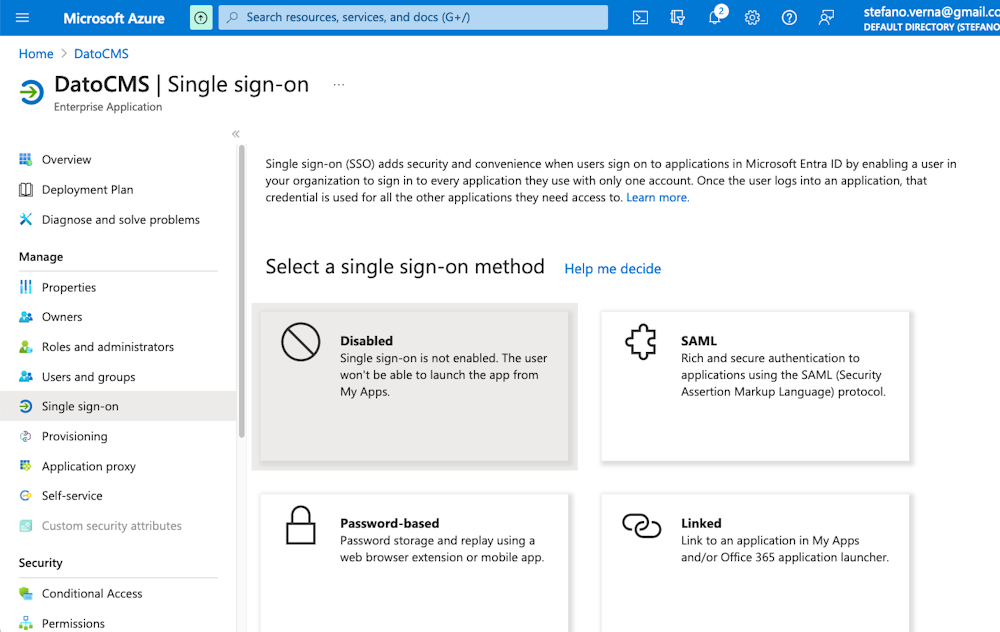
Enter the Single Sign-On section, then select SAML as single sign-on method:
Now click the small Edit button in the Basic SAML Configuration box, and fill in the following information:
Identifier (Entity ID):
https://sso.datocms.com/<YOUR_SAML_TOKEN>/saml/metadataReply URL (Assertion Consumer Service URL):
https://sso.datocms.com/<YOUR_SAML_TOKEN>/saml/consumeSign on URL (optional):
https://sso.datocms.com/<YOUR_PROJECT_ID>/saml/init
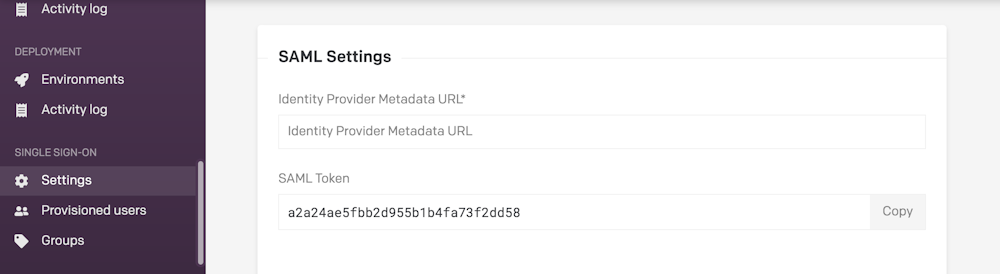
Make sure to replace <YOUR_SAML_TOKEN> with the SAML Token present in the Settings > Single Sign-On > Settings section of your DatoCMS project:
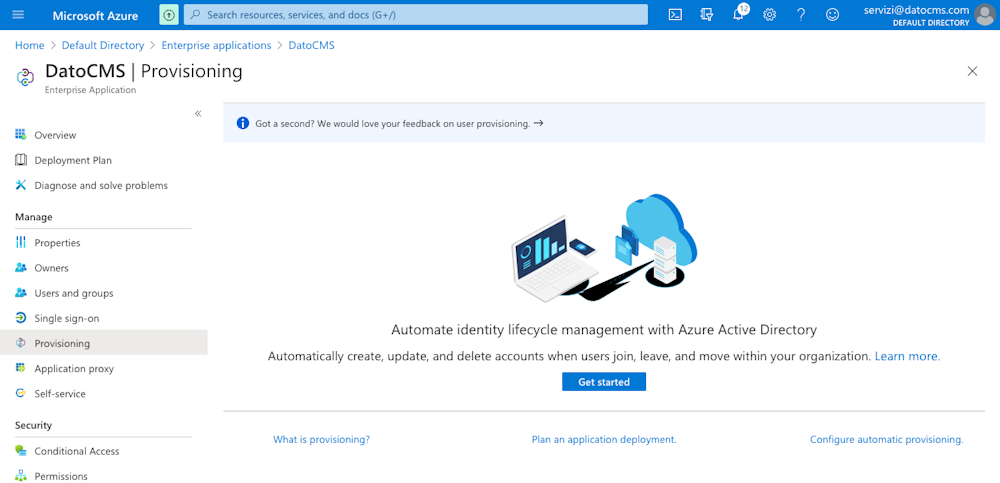
Now move into the Provisioning section, and click the Get started button:
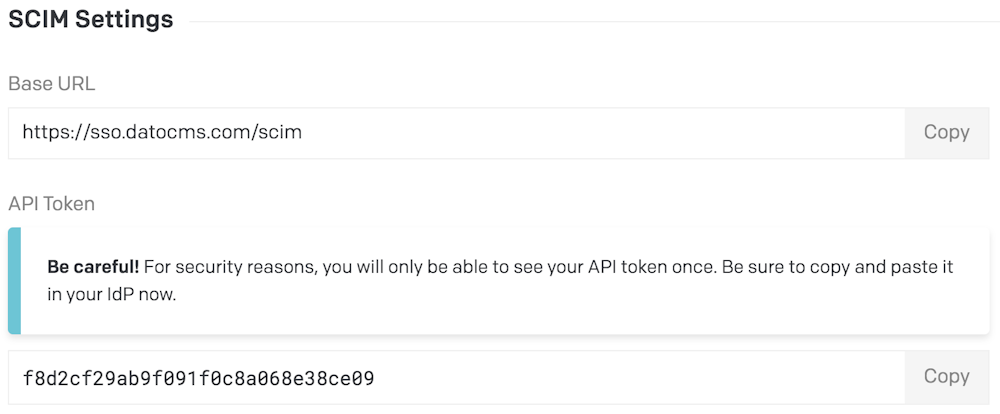
Within the Settings > Single Sign-On > Settings section of your DatoCMS project, click the SCIM Settings > API Token button:
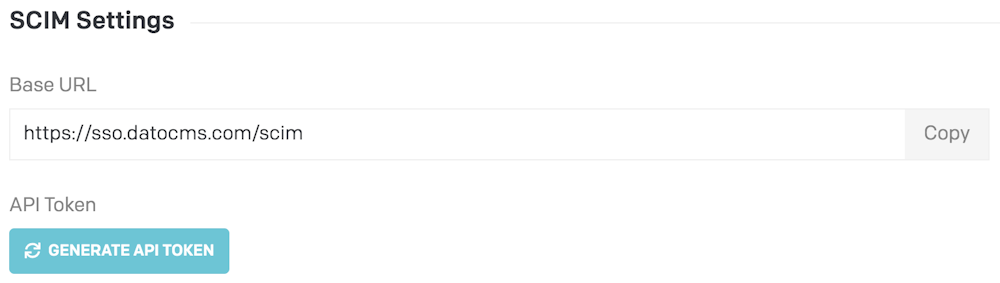
Copy the resulting API token:
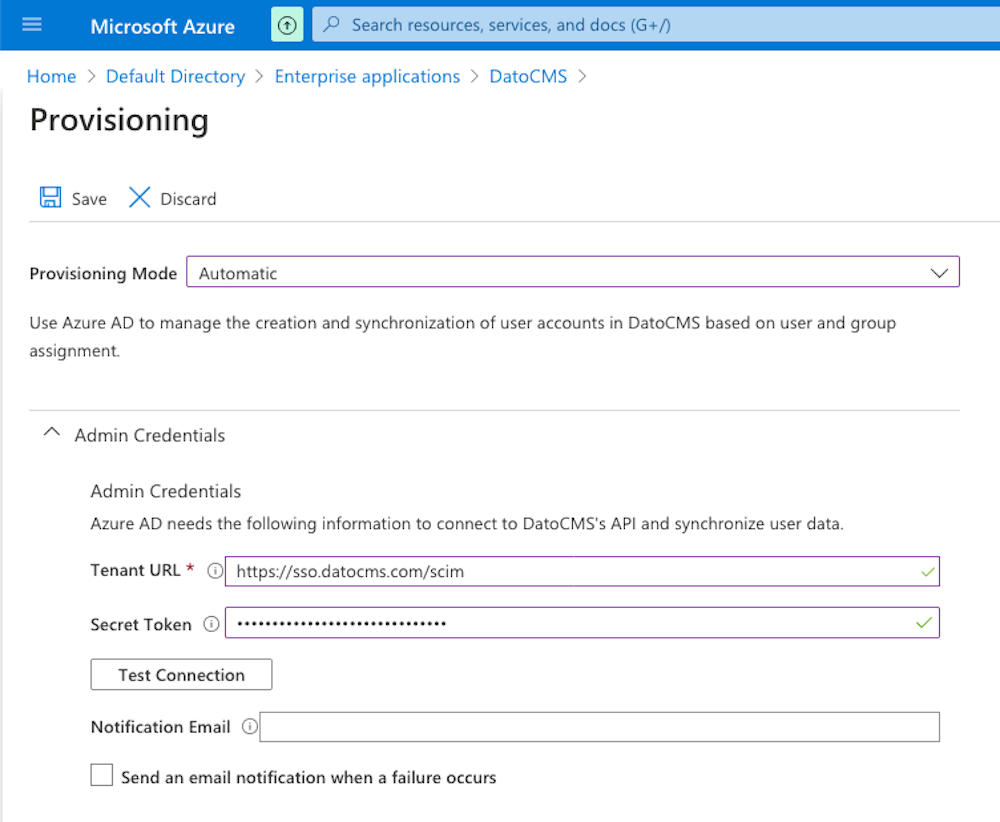
Fill in the following information:
Provisioning Mode: Automatic
Tenant URL: https://sso.datocms.com/scim
Secret Token: use the API token we generated in the previous step
Then click the Save button:
Go back to the Single Sign-On section, copy the App Federation Metadata Url...
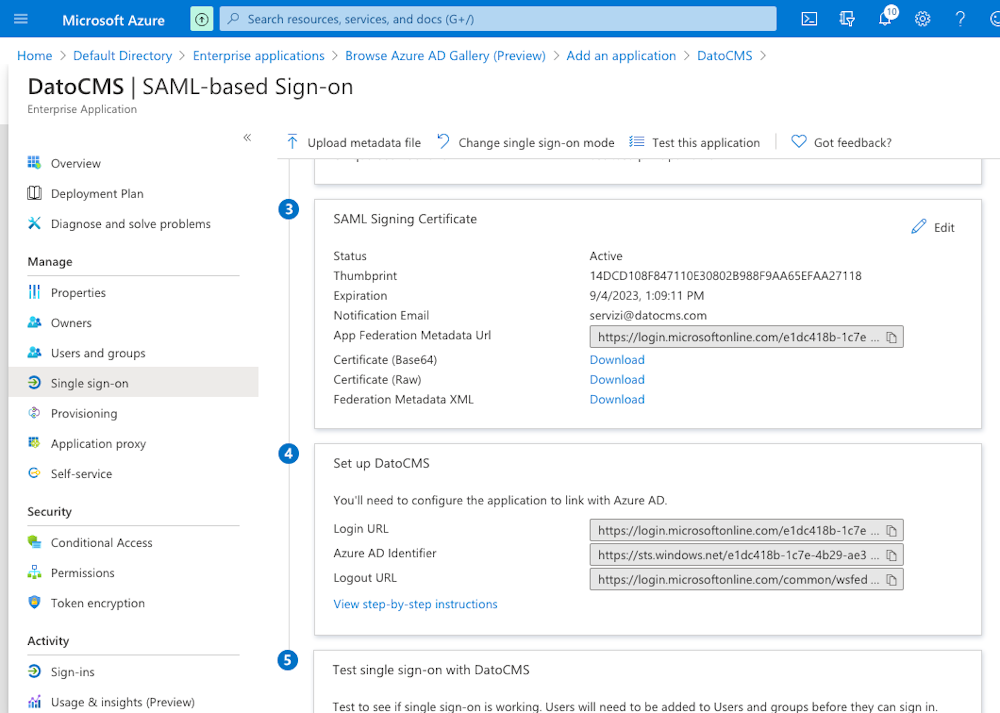
...and paste it into the DatoCMS Identity Provider SAML Metadata URL field:
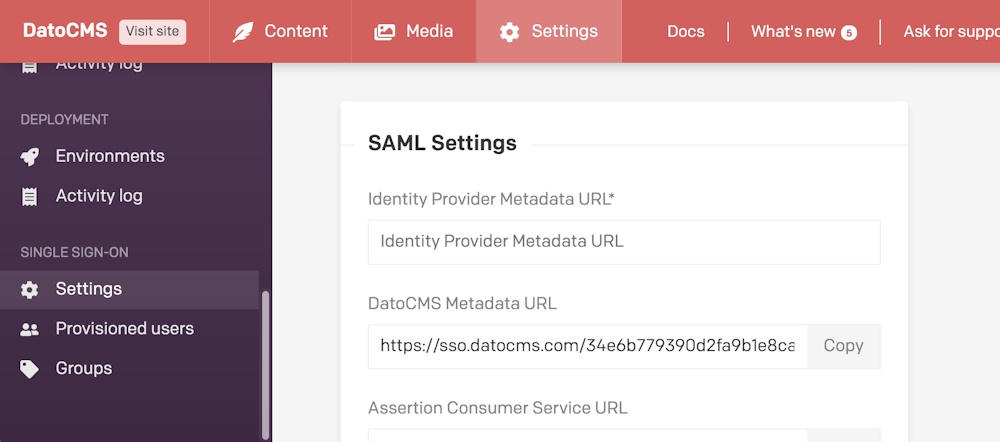
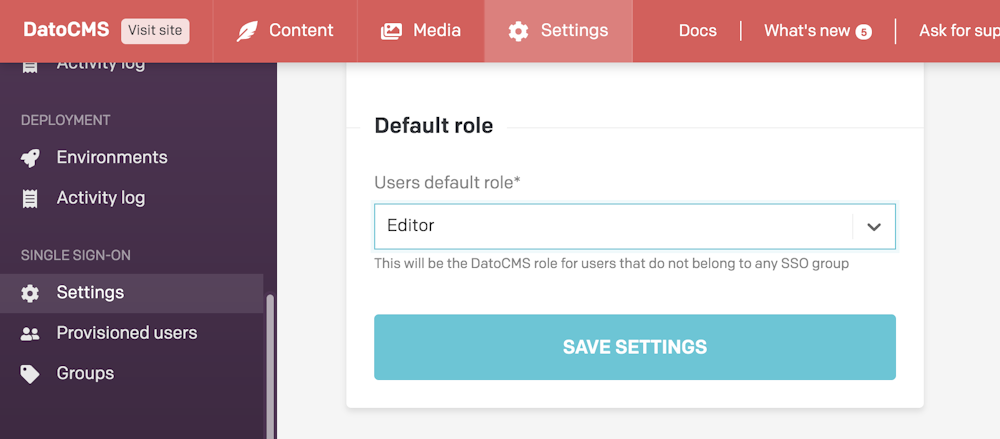
Make sure to also specify the default role editors will be assigned to (learn more about this field in the "Mapping Microsoft Entra Groups to DatoCMS roles" section below):
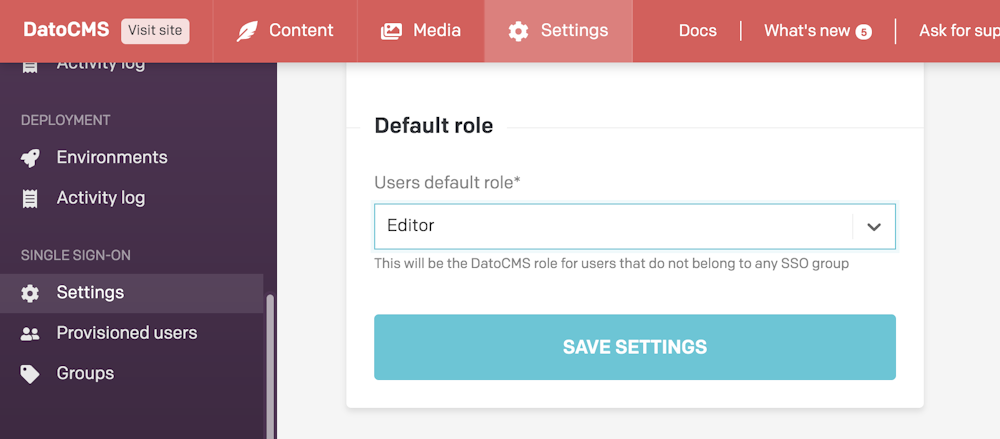
Press the Save settings button in DatoCMS.
Mapping Microsoft Entra groups to DatoCMS roles
In the Groups section in DatoCMS, you can now assign a specific role to each Group. For each group, assign the role with the same name:
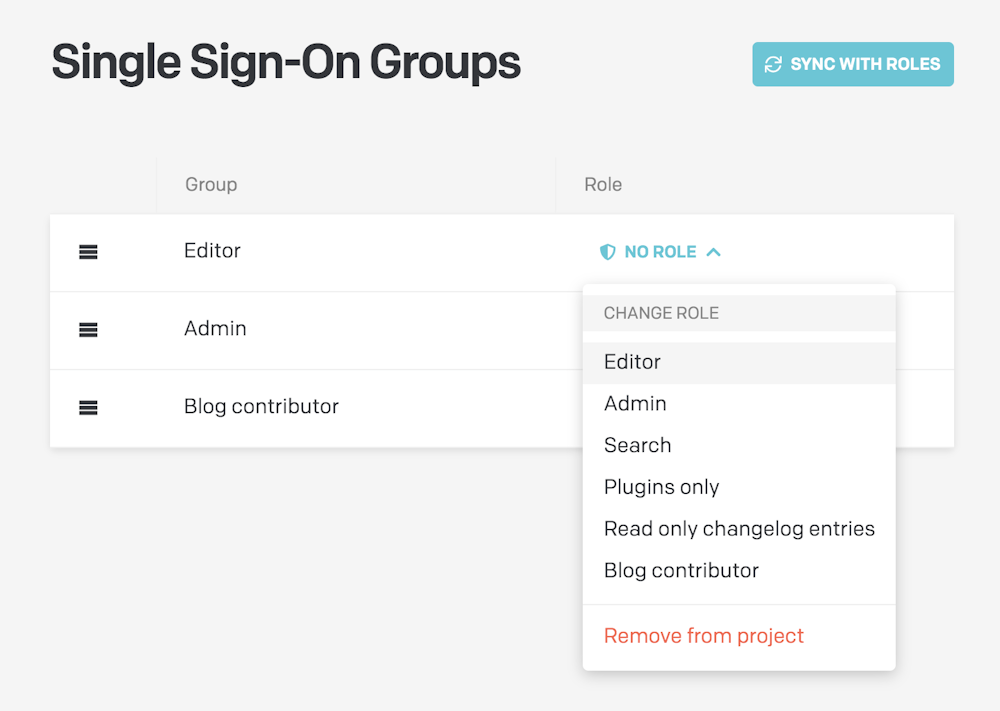
Once you've configured a role for every group, the following rules will apply:
The group's role will be applied to to every user belonging to it;
In case a user belongs to multiple groups, the first group in the list will be the one to win. You reorder groups with drag&drop to customize their priorities;
In case a user does not belong to any group, the default role specified in the SSO Settings will be used:
SAML User Attributes & Claims
DatoCMS recognizes the following claims for users (any other claim will be ignored):
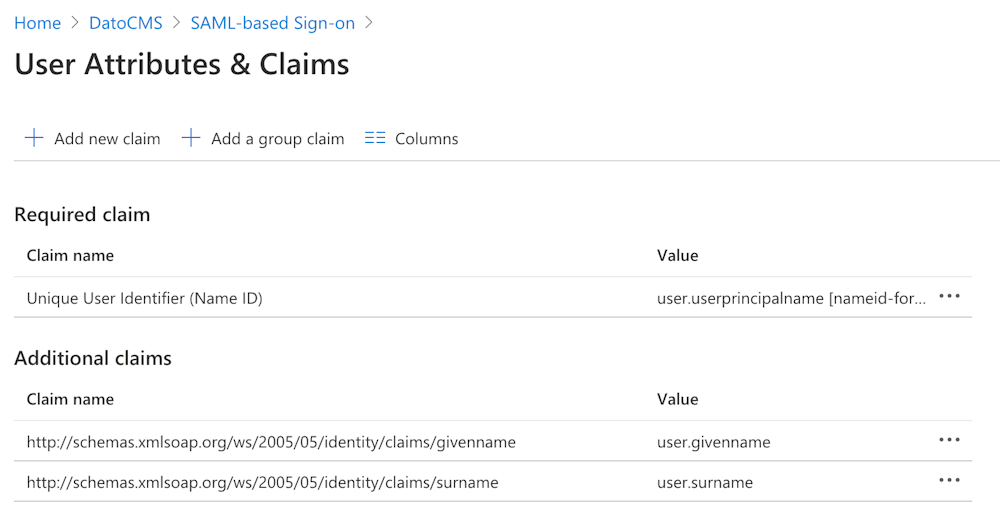
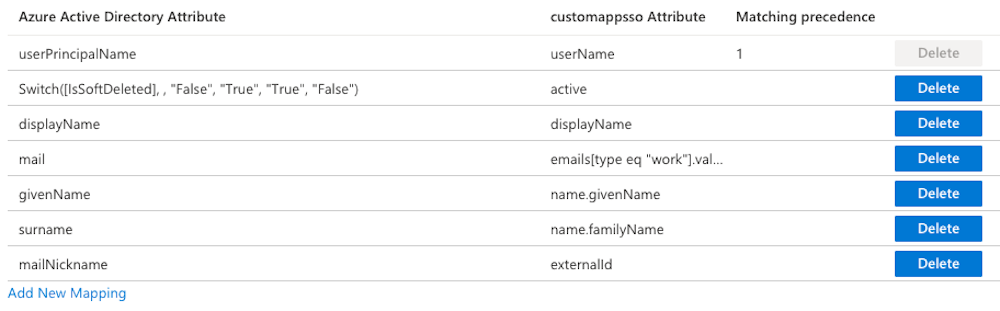
Attribute Mapping
DatoCMS recognizes the following attributes for users (any other attribute will be ignored):
Support and Troubleshooting
For any issues, please contact our support to get customized help.

