Google Workspace Single Sign-On
Enterprise integrationAutomatically provision DatoCMS users using your centralized Google Workspace
Prerequisites
Single Sign-On is only available for Enterprise plans.
Configuration Steps
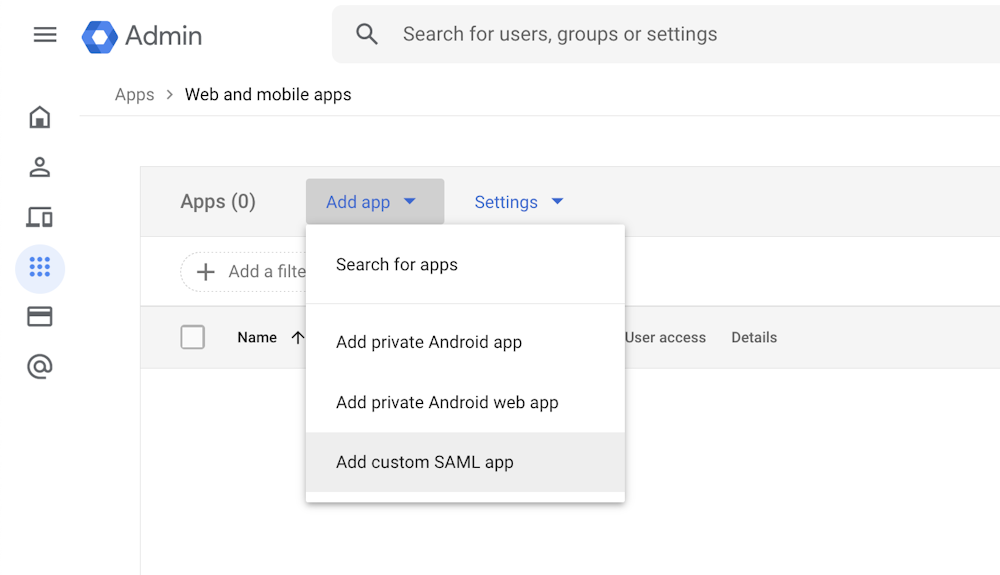
Enter your Google Admin console (at admin.google.com), go to Apps > Web and mobile apps and click Add App > Add custom SAML app.
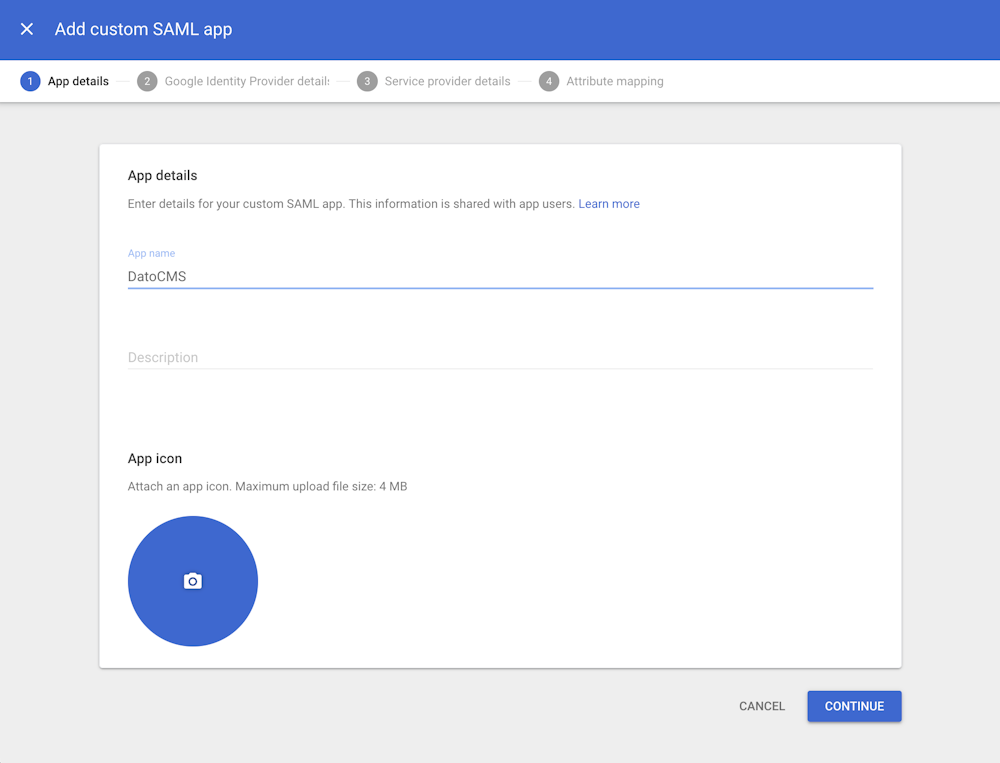
Name your application DatoCMS and click the Continue button:
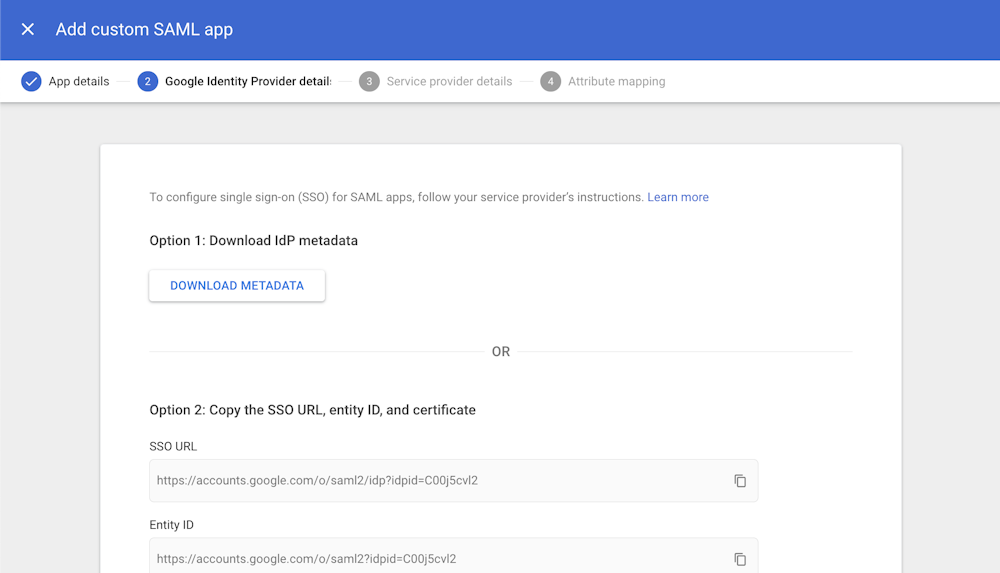
Download the IdP metadata by clicking on the Download Metadata button (we'll need this later), and click Continue:
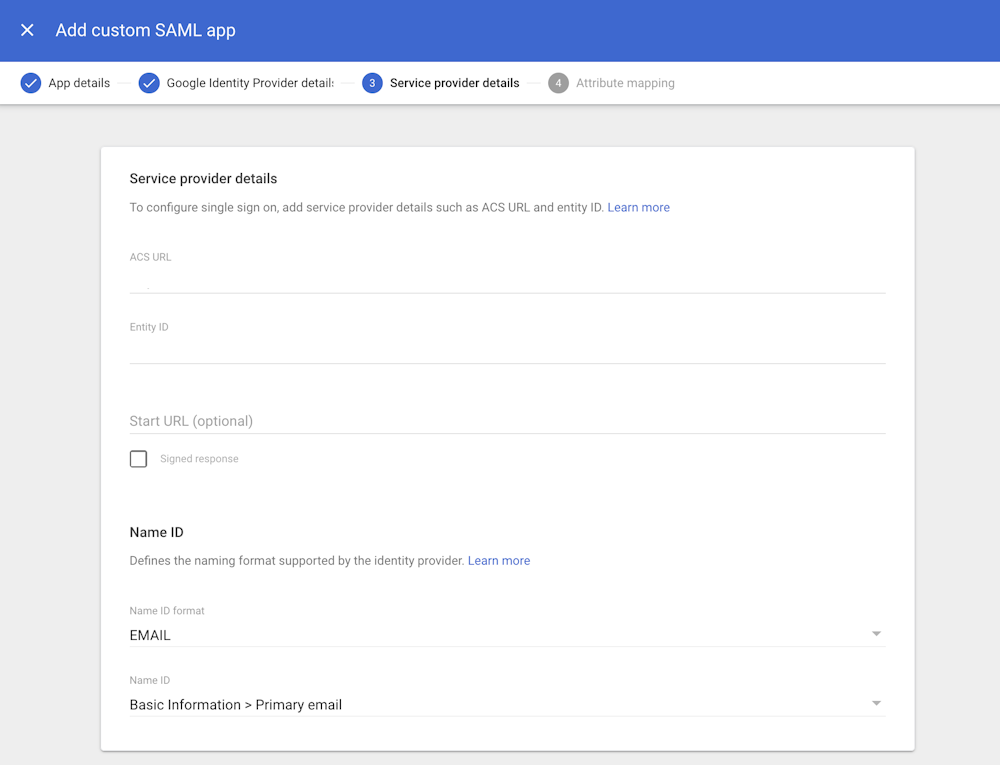
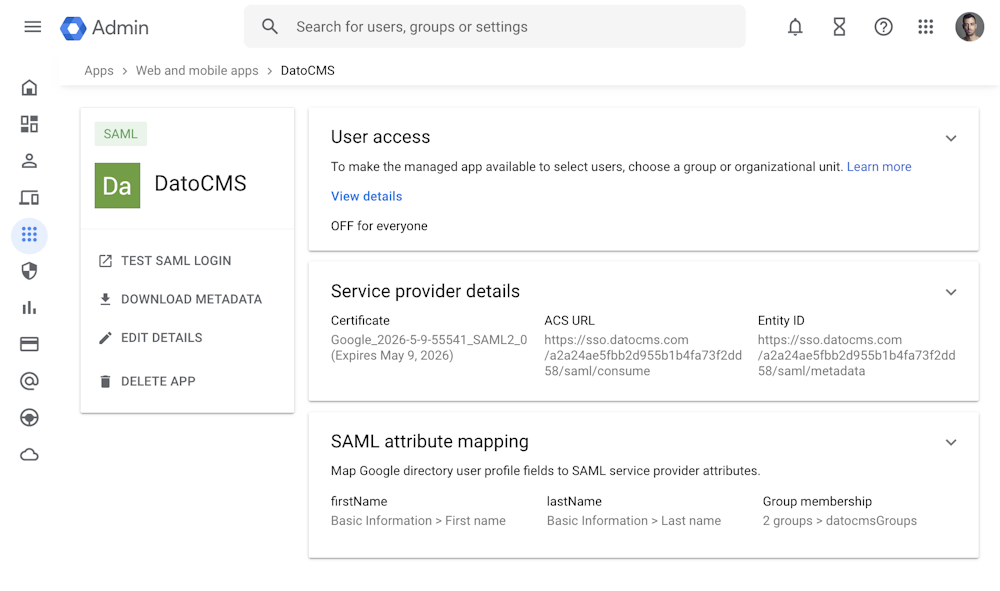
Fill in some fields using the information present in the Settings > Single Sign-On > Settings section of your DatoCMS project:
ACS URL: Copy the value of the "Assertion Consumer Service (ACS) URL" field
Entity ID: Copy the value of the "Service Provider Metadata URL / Entity ID" field
Name ID format: EMAIL
You can leave the rest of the settings as they are, and then click Continue:
In the next section, copy the following mappings:
First name:
firstNameLast name:
lastName

If you want to also activate group mapping, then select the groups you want to pass in the SAML assertion, and specify datocmsGroups as App attribute:
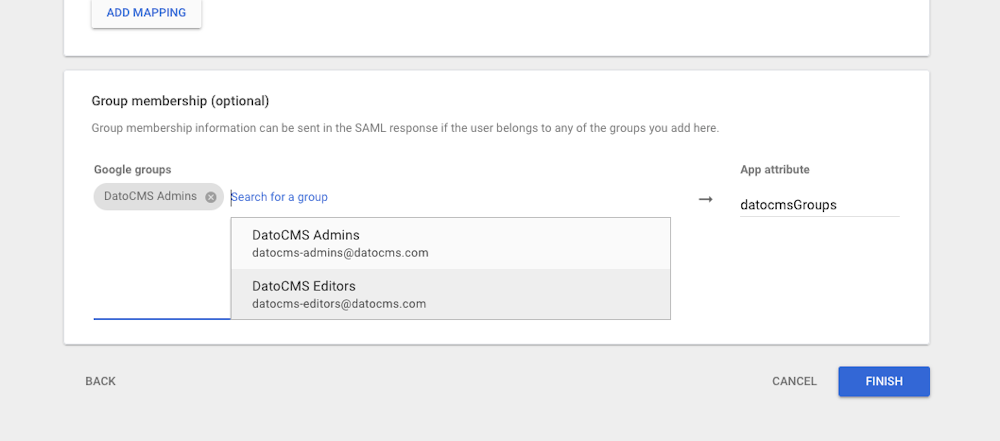
Click Finish, then activate the App by clicking on User Access, and selecting ON for everyone:
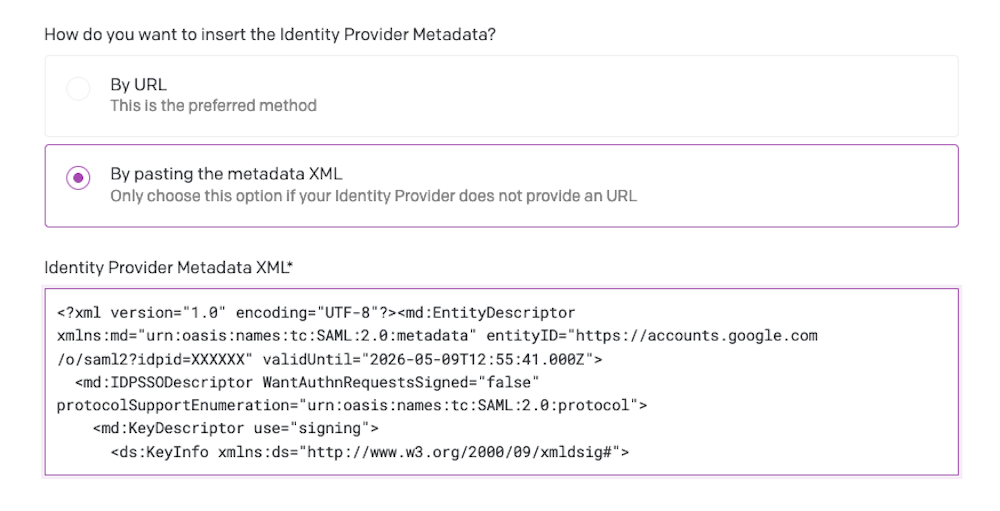
Open the IdP metadata file that we previously downloaded on any text editor.
Now, return on the Settings > Single Sign-On > Settings section of your DatoCMS project, select By passing the metadata XML, and paste the complete content of the file in the Identity Provider Metadata XML field:
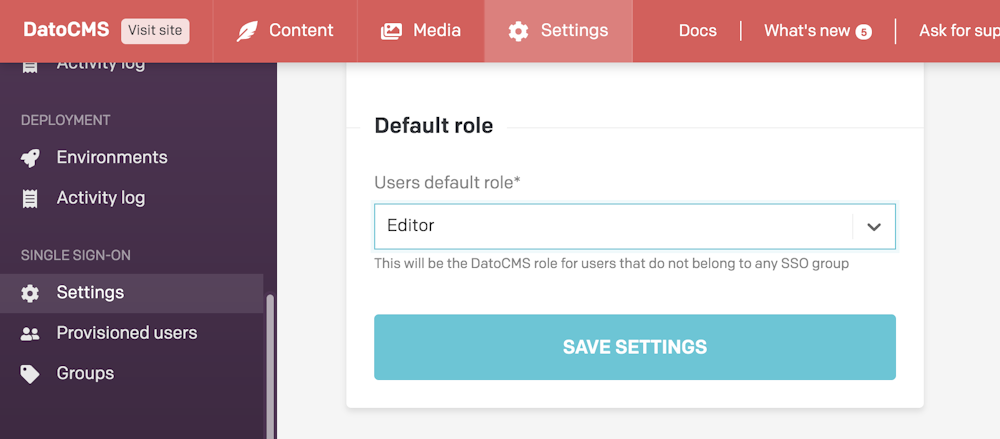
Make sure to also specify the default role collaborators will be assigned to (learn more about this field in the "Mapping groups to DatoCMS roles" section below):
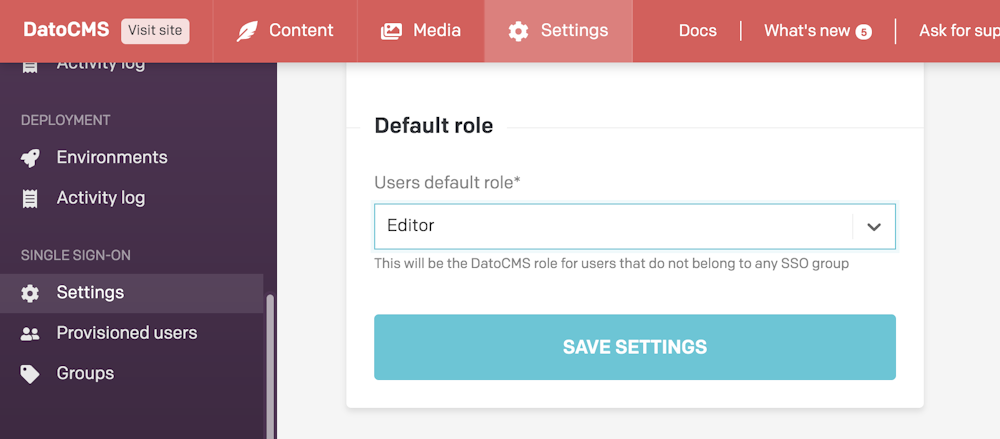
Press the Save settings button in DatoCMS.
Mapping groups to DatoCMS roles
When a user logs in using SSO, the groups it belongs to will appear in the Settings > Single Sign-On > Groups section in DatoCMS.
In this section you can assign a specific DatoCMS role to each group:
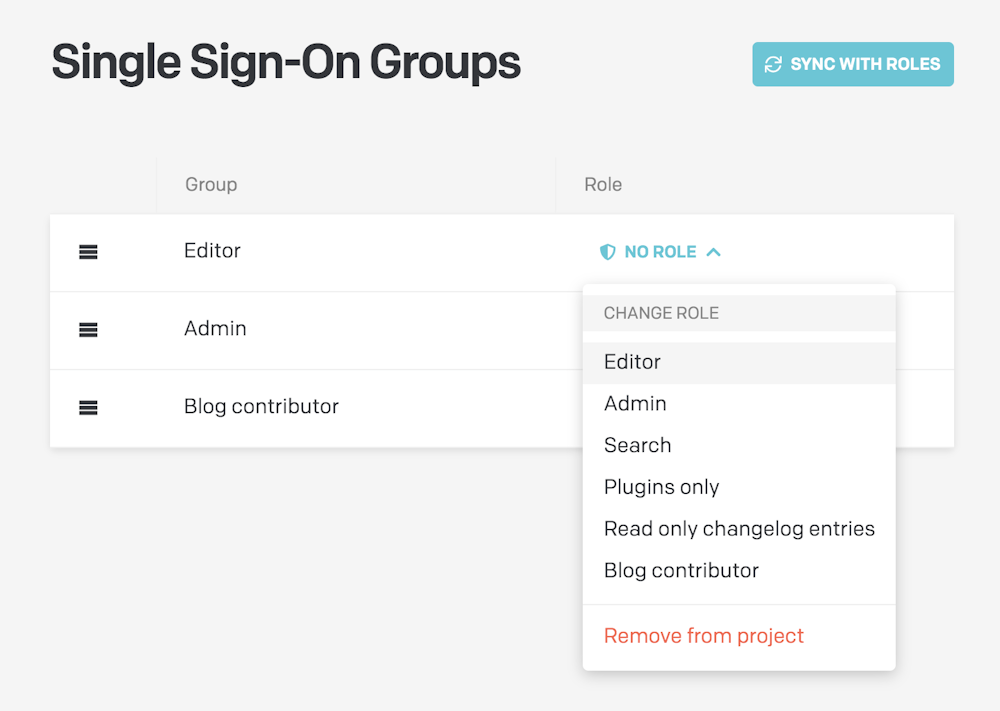
Once configured, the following rules will apply:
The group's role will be applied to to every user belonging to it;
In case a user belongs to multiple groups, the first group in the list will be the one to win. You reorder groups with drag & drop to customize their priorities;
In case a user does not belong to any group, the default role specified in the SSO Settings will be used:
Support and Troubleshooting
For any issues, please contact our support to get customized help.

